Hawk AI wins PwC Hackathon at ACAMS Hollywood 2023
In May 2023, Hawk AI participated in the PwC Hackathon at ACAMS Hollywood.
The competition aimed to identify maximum suspicious transactions and/or new trends in the provided data and artfully present our findings. Based on our company vision of streamlining the process for frontline operators and enabling them to efficiently generate high-quality true positive Suspicious Activity Reports (SARs), our data science and product teams set on working through the supplied data sets to detect financial crime.
Rather than simply identifying elements of suspicious activity that could be easily flagged, we wanted to enable the Financial Intelligence Units (FIU). Rather than mere "dumping grounds" for somewhat suspicious activity, FIUs receiving comprehensive SARs become genuine intelligence units capable of providing comprehensive and actionable insights for law enforcement agencies.
Our efforts identified various fincrime patterns in the dataset, including Collusion, Grandchild Fraud or Scam, Sanctions Evasion, Embezzlement, and more.
We employed a multi-layered approach to identify these patterns, beginning with detecting anomalous transactions and incorporating contextual information. At the transaction level, we utilize anomaly detection techniques to identify areas of concern. To provide richer context, we leverage advanced methodologies such as network analysis and clustering of word embeddings facilitated by large language models.
By integrating these strategies, we were able to expedite identifying suspicious activities, reduce the time required for frontline operators, and ultimately empower the FIU to deliver comprehensive and actionable intelligence to law enforcement agencies.
Methodology and Technology
The methodology and technology employed in our approach were designed to enhance the identification of suspicious transactions while minimizing false positives. Instead of identifying over 900 transactions as suspicious based solely on their high-risk country origin, we adopted a layered approach utilizing the following technologies:
In Layer 1, we employed anomaly detection techniques as the initial step in identifying suspicious transactions. This approach provided the foundation for suspicion and consistently achieved high accuracy across various use cases.
Layer 2 involved network analysis, which allowed us to uncover additional patterns and relationships that added contextual information to the suspicious transaction behavior. By analyzing the connections and interactions between entities, we better understand potential illicit activities.
Layer 3 leveraged the power of large language models, similar to GPT technology. This component facilitated the investigation process by incorporating internet search data. AML investigators often scrutinize internet browsing data for additional information about individuals or companies involved in suspicious activities. By ingesting and analyzing this internet search data, our system provided investigators with valuable insights and assisted in building comprehensive case narratives and profiles.
By integrating these three layers, our methodology and technology enabled us to define and identify suspicious activity more effectively. By focusing on anomalous transactions, incorporating network analysis, and leveraging large language models, we optimized the investigative process and improved the accuracy of identifying potential financial crimes within the supplied dataset.
Below are five examples of financial crime detected in the dataset:
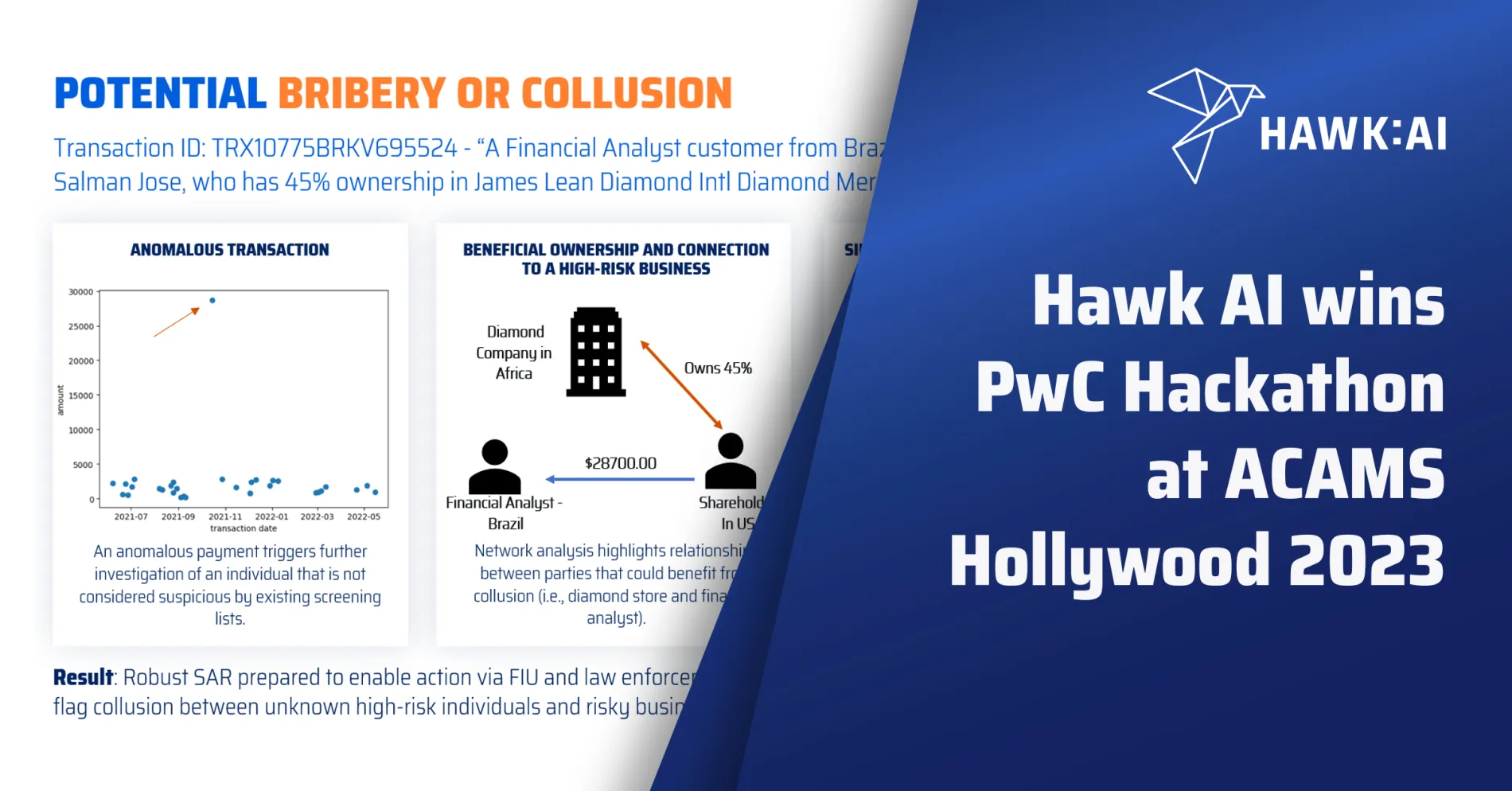
Potential bribery or collusion
In the case involving a Financial Analyst customer from Brazil receiving $28,700 from Salman Jose, who holds a 45% ownership stake in James Lean Diamond Intl Diamond Merchants registered in Africa, our investigative process revealed potential bribery or collusion. A summary of the investigation follows:
Phase 1: An anomalous payment transaction triggered a thorough investigation, despite the individual involved not being flagged as suspicious in existing screening lists. This payment raised concerns and warranted further scrutiny.
Phase 2: Network analysis techniques uncovered relationships between the parties involved, specifically focusing on potential collusion. The analysis revealed connections between the diamond store and the financial analyst, suggesting the possibility of a mutually beneficial arrangement.
Phase 3: We conducted additional research using GPT language models to enhance the investigation. This automated process provided further supporting evidence for the SAR and identified potential other cases. Using language models allowed for a comprehensive examination of the available data and facilitated the identification of relevant patterns.
Result: Our comprehensive investigation prepared a robust SAR, enabling appropriate actions by the Financial Intelligence Unit (FIU) and law enforcement agencies. Furthermore, the investigation unveiled a new behavioral model that could aid in flagging collusion between unknown high-risk individuals and risky businesses or countries. This discovery contributes to the ongoing efforts to combat financial crimes and strengthen the financial system's integrity.
Potential embezzlement or tax evasion
We observed company shareholders moving funds through intermediaries to other shareholders and/or ultimate beneficiaries, suggesting potential embezzlement or tax evasion. Our investigation yielded the following phases and outcomes:
Phase 1: Through network analysis, we identified payments made to shareholders via intermediaries, indicating a potential misuse of company resources.
Phase 2: Further network analysis revealed payments involving multiple shareholders directed toward ultimate beneficiaries. This pattern indicated a complex web of transactions aimed at transferring funds to beneficiaries through a network of shareholders, potentially concealing the true nature and purpose of the transactions.
Phase 3: In-depth network analysis uncovered circular payments made through money mule networks. This finding suggested using elaborate schemes involving money mules to obfuscate the source and destination of funds, adding another layer of complexity to the investigation.
Result: The network analysis conducted throughout the investigation demonstrated a clear flow of funds orchestrated by the owners of the businesses involved. Financial institutions can adopt these patterns and insights to strengthen their detection and prevention mechanisms. The power of this analysis increases significantly when cross-institutional information sharing becomes feasible, enabling a more comprehensive understanding of financial flows and enhancing the overall effectiveness of anti-fraud measures.
Potential sanctions evasion
In the dataset, a Receptionist, who had relocated from Russia, transferred $100,000 to a potential Politically Exposed Person. Our investigation progressed as follows:
Phase 1: An anomalous payment triggered an initial investigation, prompting a closer examination of an individual who did not raise suspicion based on existing screening lists. This payment raised concerns, prompting further scrutiny of the individual's activities.
Phase 2: Network analysis techniques revealed significant relationships between the customer, in this case, the Receptionist, and PEP entities. This analysis shed light on connections that indicated potential links to individuals with political influence, warranting further investigation.
Phase 3: In-depth counterparty investigations uncovered a pattern of frequent payments to individuals in the United States who were associated with companies in high-risk or sanctioned countries. This finding provided additional evidence suggesting potential sanctions evasion activities and raised suspicions regarding the involvement of high-risk jurisdictions or tax havens.
Result: We prepared a robust SAR. Additionally, the investigation led to the identification of a new behavioral model that could serve as a valuable tool in flagging potential sanctions evasion activities involving high-risk countries or tax havens.
Potential grandchild pattern or blackmail
We discovered money funneled out of accounts belonging to elderly individuals, with their caregivers engaging in suspicious cash-in behavior at various ATMs to conceal patterns. Our investigation discovered the following:
Phase 1: The investigation began when we detected an anomalous cash-in amount, prompting a closer examination of the pay-in behavior. We identified ATM deposits as a source of suspicion, indicating potential illicit activities.
Phase 2: Further analysis of the volume and number of terminals used for cash-ins added to the suspicion. The presence of terminals located in three different states raised additional red flags, suggesting a potential coordinated effort to facilitate the fraudulent scheme.
Phase 3: We identified regular monthly payments between the elderly individuals and their caregivers, indicating a working relationship. However, seemingly related cash-out and cash-in payments raised suspicions regarding the flow of money. These transactions indicated an attempt to obfuscate the funds' origin and destination, suggesting suspicious financial activities.
Result: Through a comprehensive analysis, we identified a clear pattern of suspicious behavior, highlighting the potential for financial crime patterns such as blackmail or "grandchild" theft.
Potential human trafficking
We discovered large amounts paid to customers associated with high-risk countries on low-volume dates such as 25 December, raising suspicions of human trafficking or sanctions evasion. Our investigation went as follows:
Phase 1: The investigation began with identifying an anomalous transaction that exhibited unusual characteristics in terms of amount volume and payment date, deviating from typical cohort behavior. This transaction stood out as an outlier, warranting further scrutiny.
Phase 2: In-depth counterparty investigations were conducted, revealing a pattern of frequent payments to individuals in the United States who were associated with companies in high-risk or sanctioned countries. These findings provided additional evidence pointing toward potential sanctions evasion activities and raised concerns regarding the involvement of high-risk jurisdictions or entities.
Phase 3: The investigation delved into the payment references, which included suspicious words that indicated a potential link to human trafficking. To further explore this aspect, a reverse investigation process was undertaken using word embeddings rather than solely relying on transaction data. This alternative approach allowed for a comprehensive analysis of the language used and helped identify potential connections and patterns related to human trafficking.
Result: The investigation identified a new behavioral model that may prove valuable in flagging potential internal collusion between unknown high-risk individuals and risky businesses or countries.
In summary
We demonstrated efficiency and effectiveness in combating financial crime by employing a multi-layered approach to technology. Using multiple layers of technology has significantly reduced the time required for frontline investigations while simultaneously enhancing the detection of true positive cases.
This increased detection rate strengthens the effectiveness of anti-fincrime measures and ensures that SAR filings are of higher quality, providing comprehensive and actionable insights for FIUs and law enforcement agencies.
To learn more about Hawk AI, access our content library with deep dives into topics including using anomaly detection, entity resolution, and AI to fight financial crime.